You don’t have to be Fortune 500 to be on a hacker’s radar. In fact, being small might be exactly why you’re on it.
Let’s settle something right now. If you’re a small business owner, a COO, or a security leader at a mid-sized company and you still believe your organization is too small to be worth a hacker’s time — that belief is not just wrong. It is actively dangerous. And it may already be costing you.
The data from 2025 and early 2026 is unambiguous: cybercriminals have made a strategic pivot. Large enterprises — with their deep security budgets, dedicated SOC teams, and enterprise-grade tooling — are increasingly hardened targets. So attackers went looking for softer ground. They found it in small and mid-sized businesses.
This is not a coincidence. It is a calculated business decision made by criminal organizations that operate with more sophistication and efficiency than most SMBs’ entire IT departments. Understanding why you’re a target — and what they’re counting on — is the first step toward not becoming a statistic.
The Numbers Don’t Lie — And They’re Alarming
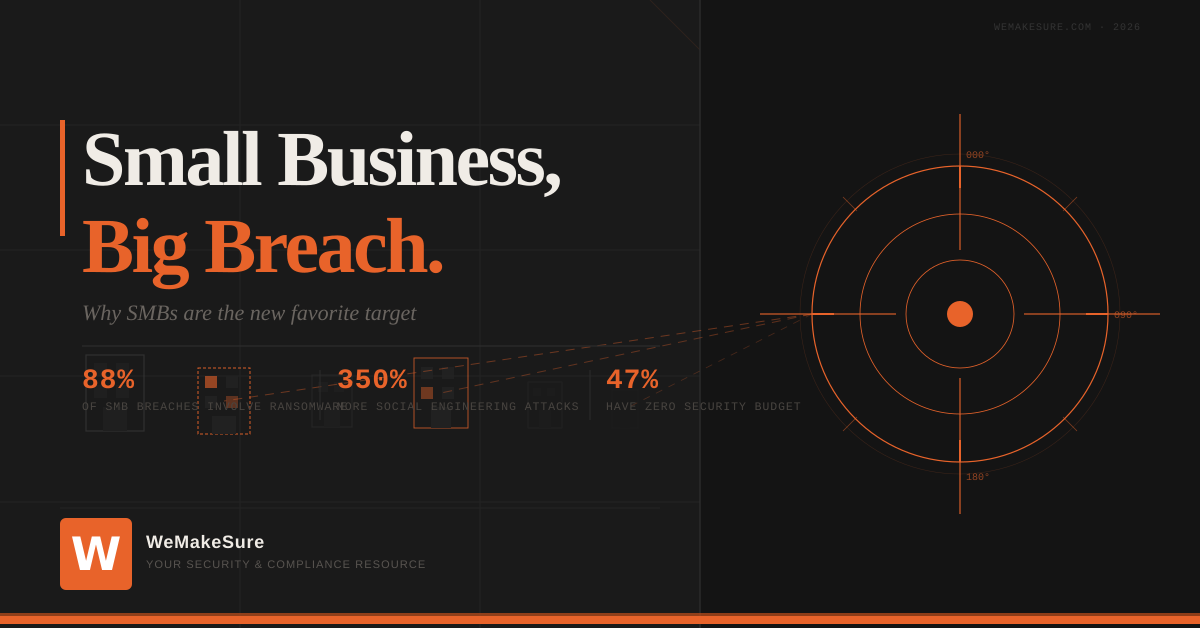
Before we get into the why, let’s look at the scale of what’s happening. These aren’t projections. These are reported figures from 2025.
Read those numbers again. Nearly nine out of ten breaches at small businesses involve ransomware. Your employees are targeted for social engineering at three and a half times the rate of enterprise workers. And nearly half of the smallest businesses have budgeted exactly nothing for cybersecurity.
To threat actors, that last statistic is an open invitation.
Why Hackers Chose You Over the Big Fish
Here’s a way to think about this. Ransomware operators run businesses. They have revenue goals, risk tolerances, and operational efficiency targets just like anyone else. When they evaluate targets, they make rational economic calculations.
“Large enterprises are increasingly hardened targets with deep IT budgets and dedicated security teams. Going after them is like trying to rob a bank with armed guards. Small businesses? Many are running on outdated systems, stretched-thin staff, and the IT equivalent of a screen door.”
The math works in their favor when they target SMBs. Lower ransom expectations — but dramatically higher success rates. Attackers have industrialized this model through Ransomware-as-a-Service (RaaS) platforms, where criminal developers lease their malware to affiliates who need only basic skills to execute attacks. The result is that serious ransomware capabilities that once required significant technical sophistication are now effectively commoditized and pointed directly at businesses like yours.
One ransomware operation, Qilin, executed over 1,000 attacks in 2025 alone — a 408% increase over prior years — using exactly this model. Your company doesn’t need to be a household name to be in their crosshairs. You just need to be reachable, understaffed on security, and carrying data someone would pay to recover.
Three Reasons You’re More Exposed Than You Think
1. Your Employees Are the Primary Attack Vector
According to the World Economic Forum, 95% of cybersecurity breaches are attributed to human error. Phishing emails, credential theft, and social engineering don’t discriminate by company size — but they disproportionately succeed where security awareness training doesn’t exist. In 2025, small businesses received malicious emails at a rate of 1 in every 323 emails. That’s 2.3 times the rate at larger organizations.
If your team hasn’t completed structured security awareness training recently, they are — right now — your biggest vulnerability.
2. You’re a Gateway to Larger Targets
Supply chain attacks nearly doubled in 2025, with a 93% year-over-year increase in reported incidents. Attackers increasingly target smaller businesses not just for the data they hold directly, but because they serve as a bridge to larger partners and customers. If your business touches healthcare data, financial systems, or enterprise software platforms, you may be the path of least resistance into a much bigger breach.
According to Group-IB’s High-Tech Crime Trends Report 2026, supply chain attacks have become the dominant force reshaping the global threat landscape. A single compromised vendor relationship can expose an entire industry. Your security posture doesn’t just affect you — it affects every organization you do business with.
3. The Window Between Breach and Detection Is Wide Open
IBM’s Cost of a Data Breach Report found that the average breach takes 204 days to identify globally. For small businesses — which rarely have continuous monitoring, endpoint detection tools, or incident response plans — that window is likely longer. Attackers aren’t smashing and grabbing anymore. They’re entering quietly, mapping your network, elevating privileges, and positioning themselves for maximum impact before you ever see a warning sign.
By the time ransomware deploys, the attacker has often been inside your environment for weeks.
What a Breach Actually Costs a Small Business
Every executive wants to know the number. Here it is: the average SMB breach cost sits between $120,000 and $1.24 million, according to Verizon. IBM puts the average cost for businesses with fewer than 500 employees at $3.31 million when all factors are accounted for — downtime, legal fees, regulatory penalties, customer notification, reputational damage, and lost business.
But the headline number only tells part of the story. VikingCloud research shows that downtime from a cyberattack costs businesses approximately $53,000 per hour. If your systems are down for 24 hours — a common scenario in ransomware events — you’re looking at over $1.2 million in downtime costs alone, before a single recovery expense.
And 75% of SMBs that are hit with ransomware say they could not continue operating if the attack succeeded. That’s not a financial risk. That’s an existential one.
The Preparedness Gap Is Where Businesses Die
Here is perhaps the most sobering finding from the Guardz 2025 SMB Cybersecurity Report: 80% of SMBs that had a formal incident response plan in place were able to avoid major damage during an attack. The plan itself — not more expensive tools, not a bigger security team — was the differentiating factor.
Yet only 26% of small businesses have a formal incident response plan at all.
The plan itself — not more expensive tools, not a bigger security team — was the differentiating factor. 80% of SMBs with a formal incident response plan avoided major damage. Only 26% have one.
Additionally, 52% of SMBs still rely on an untrained internal staff member or the business owner themselves to manage critical security functions. This is the equivalent of asking your office manager to perform surgery because you can’t afford a doctor — and then being surprised when the patient doesn’t recover.
Five Things Every SMB Executive Should Do Today
This isn’t about spending your way to safety. Many of the highest-impact steps cost little to nothing. What they require is intentionality and follow-through.
- → Build and test an incident response plan. Document who does what when a breach occurs. Test it at least annually. Organizations with a tested IR plan save an average of $232,000 per breach event. The plan is free to create.
- → Implement multi-factor authentication everywhere. Stolen credentials are among the top entry points for ransomware. MFA alone reduces successful attacks by up to 90%. There is almost no justification for not having it in place today.
- → Train your employees — regularly. Quarterly phishing simulations and security awareness training deliver the highest ROI of any security measure. Your people are either your first line of defense or your primary vulnerability. Training is what determines which one.
- → Establish a 3-2-1 backup strategy. Three copies of your data, on two different media types, with one copy offsite. Ransomware-resistant backups eliminate the attacker’s primary leverage. This strategy costs under $500 per year for most small businesses and completely changes the calculus of a ransomware demand.
- → Audit your vendor and third-party relationships. Ask every critical vendor about their incident response capabilities, security certifications, and breach history. Your security posture is only as strong as your weakest integration. If a vendor can’t answer basic security questions, that’s your answer.
The Bottom Line for Leaders
The conversation around cybersecurity in small and mid-sized businesses has changed. It is no longer a question of whether you will face a threat. The data from 2025 and 2026 makes clear that you already are. The question is whether your organization is positioned to survive it.
Cybercriminals have made their choice. They’ve evaluated the risk-reward ratio and decided that businesses like yours — with real data, real customer relationships, and often thin security defenses — represent their best opportunity. That is a problem that executive awareness, organizational commitment, and a few well-placed investments can meaningfully address.
The businesses that make it through a breach aren’t necessarily the ones with the biggest security budgets. They’re the ones that took the threat seriously before it arrived, built the right habits, and had a plan ready when they needed it.
That work starts today. Not after the audit. Not after the next budget cycle. Today.
Is Your Business Ready for What’s Coming?
We Make Sure helps organizations build security and compliance programs that hold up when it matters most. Start the conversation before a breach forces it.